|
Hello Tor community,
This month, we decided to write a slightly different newsletter. We want to answer questions you may have regarding news about Tor’s security.
First, Tor is a secure tool to use. For perspective on how the Tor Project makes decisions about security and development, we’ll start with a tweet from Edward Snowden:
I wouldn’t expect any system to be totally secure, much less remain secure forever in the face of adversary advances, but that is not the claim. Security is the process of choosing between “less safe” and “more safe’” and continuing to fork towards safety until you reach “safe enough.”
Snowden is right. Like all software, Tor development is a process. The Tor daemon, Tor Browser, onion services, pluggable transports, and many other software we develop are just like any other piece of software — they will have bugs. We are always working to make Tor safer for the largest number of users by prioritizing the most impactful changes.
In that spirit, we’d like to talk about two clusters of reports and the action we’ve taken.
1. You may have heard about a series of bugs in Tor being reported as “0-days.” These bugs aren’t 0-days. Many of them are open in our bug tracker. We have triaged these tickets and determined they are not high priority, and they do not harm our users' anonymity. We explained more about our decision process regarding these bugs, and what comes next, in a tweet.
2. You may have heard about a group of exit relays running sslstrip attacks on the Tor network in May and June 2020. This attack targeted unencrypted HTTP connections to a small number of cryptocurrency exchange websites, and left other traffic alone. These relays have been monitored and excluded from the Tor network since they’ve joined. You can read the full details about the attack, and the next steps to mitigation, on our blog. Monitoring the Tor network continuously is very important in catching these kinds of attacks, and given our limited capacity, you can help by donating to help increase our network monitoring capacity, running your own relay, or reporting bad relays.
These reports point to some truths about the Tor Project: (1) We have finite capacity, which has been exacerbated by the financial need to lay off 1/3 of our staff in April. (2) Given our finite capacity, we have to triage and prioritize the work that has the highest impact for our users. (3) We can improve communication with our volunteers, contributors, and users so that our decision making process, and the priority of user security, is more clear. Like this newsletter.
Our blog is another important resource for updates on what’s happening in the Tor world, and is one of the places we will use to improve our communication. This month we published a blog post outlining the two methods we are considering to mitigate DDoS attacks on the Tor network, which is an example of how we like to discuss problems and potential solutions. We’ve also begun posting monthly reports on anti-censorship activities so you can keep up with our work in this area.
We believe that transparency builds trust. Our work is available for anyone to review and use to learn about Tor. Our code is open. Our development meetings and discussions are open on IRC and mailing list. We welcome those who would like to help review our work for security issues, and when they are found, to use responsible disclosure to report them.
Isabela Bagueros
Executive Director
Final day to donate to the Bug Smash Fund
Today, August 31, is the final day of the Bug Smash Fund campaign. We owe you a big thank you. This campaign has been more successful than 2019’s, even though we had to overcome a loss of donations from cancelled in-person events. If you haven’t made a contribution to the Bug Smash Fund, and want to help us build a reserve of funds that goes towards finding and fixing bugs and conducting routine maintenance, you still have a chance. Make a donation before the end of the day on August 31, and your contribution will help us smash all the bugs.
End of #MoreOnionsPorFavor campaign
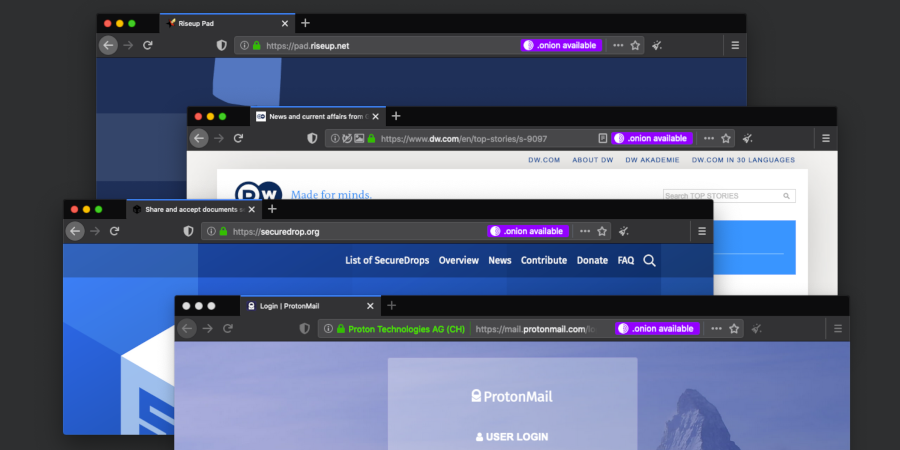
Over the last month, onion services operators and our broad community celebrated and deployed a brand new feature called Onion-Location. The feature, a purple pill in the URL bar, advertises to users that there’s a more secure way to connect to a site by using onion services. Over 60 organisations and individuals -- small, medium, and large onions -- have reached out to us to be part of this campaign. Read more about the success of the #MoreOnionsPorFavor.
New Releases
This release ships with Firefox 78.2.0esr, and updates NoScript to 11.0.39. Full changelog.
This release updates Firefox to 68.12.0esr, NoScript to 11.0.38, and HTTPS Everywhere to 2020.08.13. Full changelog.
This release ships with Firefox 78.1.0esr but there are a lot more changes that we included compared to the previous alpha version. Full changelog.
Tor 0.4.4.4-rc is the first release candidate in its series. It fixes several bugs in previous versions, including some that caused annoying behavior for relay and bridge operators. Full changelog.
What We're Reading
"Así logramos que el más grande operador de telecomunicaciones mexicano dejara de bloquear la internet segura," GlobalVoices.
"A quarter of the Alexa Top 10K websites are using browser fingerprinting scripts," ZDNet.
"Roger Dingledine of the Tor Project talks privacy and COVID-19 apps," Avast.
"Poll reveals Americans data privacy frustrations," Axios.
"A new technique can detect newer 4G 'stingray' cell phone snooping," Tech Crunch.
"The Age of Mass Surveillance Will Not Last Forever," WIRED.
Events with Tor
Join Our Community
Getting involved with Tor is easy. Run a relay to make the network faster and more decentralized. Run a bridge to help censored users access Tor.
Learn about each of our teams and start collaborating.
Donate to help keep Tor fast, strong, and secure.
|
